Manufacturing remains the world's most ransomware-targeted sector for the fourth consecutive year, with incidents surging 61% in 2025, according to cybersecurity analysts tracking OT environments1cybersecurity analysts tracking OT environments. At the same time, the industrial enterprises absorbing that threat pressure are deploying AI copilots and connected worker platforms at an accelerating pace - embedding intelligence directly into Manufacturing Execution Systems (MES), SCADA networks, and frontline workflows. The result is a fundamental rewrite of how operators, engineers, and enterprise systems interact: one that creates measurable productivity gains and an equally measurable expansion of the industrial attack surface.
Understanding how these forces intersect is now a strategic imperative for operations and OT security leaders alike.
AI Copilots Enter the MES Layer
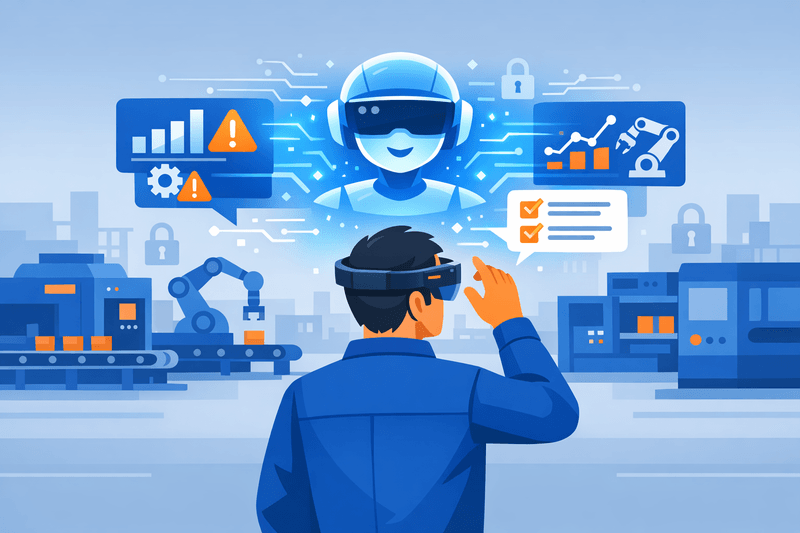
The emergence of AI copilots as a native MES capability marks a significant departure from traditional operator interfaces. Rather than navigating layered menus or waiting for engineering support, operators can query production systems in natural language and receive contextual, data-driven responses in seconds.
Natural-language querying, instant data visualizations, and contextual explanations of MES information2Natural-language querying, instant data visualizations, and contextual explanations of MES information represent a new operational paradigm - one where knowledge that once resided in experienced engineers is surfaced to any authorized worker on demand. Platforms in active deployment allow operators to ask questions such as "What happened on the night shift that I need to know about?" or "What were the top reject reasons on Line 4 this week?" and receive structured, actionable answers drawn from governed production data.
This capability addresses one of the sector's most persistent structural problems: the skills gap. Industrial leaders facing growing skills gaps, legacy processes, inconsistent quality, and labor shortages are increasingly turning to AI copilots3Industrial leaders facing growing skills gaps, legacy processes, inconsistent quality, and labor shortages are increasingly turning to AI copilots to deliver institutional knowledge to less-experienced workers in real time. At Siemens, more than 120,000 engineers now leverage industrial copilots to upskill and accelerate their work, according to Automate 2025 reporting4Automate 2025 reporting.
The enterprise footprint is expanding quickly. Siemens unveiled its Engineering Copilot for TIA Portal at SPS 2025, capable of autonomously executing complex engineering tasks5Siemens unveiled its Engineering Copilot for TIA Portal at SPS 2025, capable of autonomously executing complex engineering tasks including code generation, visualization development, and workflow automation. Microsoft's Factory Operations Agent6Factory Operations Agent, available through Azure AI Foundry, enables operators and production leaders to access MES insights, monitor OEE, and automate root cause analysis through natural language prompting across more than 160 languages.
What Separates Industrial Copilots From Generic AI
A critical distinction governs whether an AI copilot is fit for shop-floor deployment. Industrial copilots read manuals, engineering drawings, maintenance logs, standard operating procedures, and historical production data4Automate 2025 reporting - not the open internet. That grounding in proprietary operational context separates a generalist AI assistant from a production-relevant decision-support tool.
This distinction also shapes the required security architecture. Access to an AI copilot connected to live MES data is, by extension, access to production-sensitive operational intelligence. Governance of that access is not optional.
The Comparison: AI Copilot vs. Traditional MES Workflow
| Capability | AI Copilot in MES | Traditional MES Workflow |
|---|---|---|
| Operator interface | Natural-language queries and conversational prompts | Menu-driven navigation through structured screens |
| Alert triage | AI-ranked priority with proposed corrective actions | Raw alarm list requiring manual operator interpretation |
| Knowledge transfer | Contextual guidance delivered in real time to any worker | Dependent on experienced staff availability |
| Anomaly detection | Continuous ML-driven pattern recognition across data streams | Rule-based threshold alerts with limited context |
| Root cause analysis | Automated suggestion with audit trail | Manual investigation by engineers |
| Security posture | Requires governed AI models, access controls, and telemetry monitoring | Standard IT/OT access controls and network segmentation |
Connected Worker Ecosystems: Capability and Attack Surface in One Package
AR headsets, smart helmets, body-worn cameras, and wearable sensors now form an operational layer between frontline workers and the digital systems governing production. From logistics workers wearing smart helmets to field engineers using AR headsets for live assistance, the benefits are tangible7From logistics workers wearing smart helmets to field engineers using AR headsets for live assistance, the benefits are tangible. Faster troubleshooting, accelerated knowledge transfer, and real-time procedural guidance are measurable outcomes already documented across multiple industrial deployments.
The security implications, however, are equally concrete. Each connected wearable represents another node on the corporate network - another potential entry point for attackers7From logistics workers wearing smart helmets to field engineers using AR headsets for live assistance, the benefits are tangible. These devices continuously collect and transmit operational data, often through manufacturer-managed cloud platforms that sit outside direct enterprise control. In environments where non-traditional devices like wearables and rugged industrial scanners often fly under the cybersecurity radar8non-traditional devices like wearables and rugged industrial scanners often fly under the cybersecurity radar, the risk of unpatched endpoints serving as lateral movement vectors into OT networks is substantial.
⚠️ Security Gap Alert: Organizations should treat AR headsets, smart helmets, and body-worn sensors as regulated endpoints - not consumer accessories - subject to the same access controls, network segmentation policies, and continuous monitoring applied to OT assets. In zero-trust architectures, device identity validation and automated access revocation for unpaired or lost devices are baseline requirements.
OT/IT Convergence: The Business Driver Creating Security Debt
The business case for OT/IT convergence is well established. Connecting OT systems to enterprise IT enables real-time production analytics, predictive maintenance, remote diagnostics, and tighter supply chain integration1cybersecurity analysts tracking OT environments. By 2025, over 75% of leading manufacturers had implemented some form of IT/OT convergence, according to analysis of the Fortinet State of Operational Technology and Cybersecurity Report.
The security debt accumulating in parallel, however, is significant. The convergence of IT and OT and the integration of AI in OT have required a fundamental rethinking of industrial security9The convergence of IT and OT and the integration of AI in OT have required a fundamental rethinking of industrial security, creating new and complex attack surfaces that legacy OT security models were not designed to handle. In Q1 2025 alone, Honeywell reported over 2,400 ransomware attacks, with the OT layer being the prime target, compared to 6,130 incidents across all of 2024 - a sharp upward trend.
IT/OT convergence gives malicious actors easier access to previously air-gapped OT environments and exposes legacy systems to modern threats10IT/OT convergence gives malicious actors easier access to previously air-gapped OT environments and exposes legacy systems to modern threats. The pathway from compromised enterprise email to live production control systems is increasingly well-documented. Lateral movement from compromised enterprise IT networks represents the most common attack vector into industrial control systems11Lateral movement from compromised enterprise IT networks represents the most common attack vector into industrial control systems, according to the SANS Institute.
For manufacturers evaluating MES platform strategies, the related analysis in MES Platforms Unite OT and IT at Hannover Messe 2026 and Cloud-Native MES and IT/OT Convergence Reshape Manufacturing Security Posture provides relevant context on how vendors are approaching unified data governance across the OT/IT boundary.
Security Governance for AI in OT: The New Baseline
Deploying AI copilots in OT environments introduces a category of risk that extends beyond network security. Model behavior, data provenance, and explainability become operational concerns when an AI recommendation can influence scheduling decisions, quality dispositions, or corrective maintenance actions.
As of 2025, only approximately 10% of ICS/OT environments currently use AI tools, according to Rockwell Automation's OT cybersecurity research12Rockwell Automation's OT cybersecurity research - but enterprise intent is accelerating. 49% of manufacturers plan to use AI and machine learning for cybersecurity, up from 40% in 2024, per Rockwell's State of Smart Manufacturing Report13Rockwell's State of Smart Manufacturing Report.
The emerging governance baseline for AI copilots in production environments includes several non-negotiable components:
- Least-privilege access: AI services should operate with the minimum data permissions required for their function. A scheduling copilot does not need access to quality or ERP financial data.
- Containerized and auditable deployments: AI models should run in isolated containers with full logging of inputs, outputs, and model version history to support both operational auditing and incident investigation.
- Behavioral telemetry: Continuous monitoring of model behavior - not just network telemetry - is required to detect drift, misconfiguration, or adversarial manipulation of AI recommendations.
- Human validation gates: In safety-critical or high-consequence processes, AI-proposed actions should require human confirmation before execution. Automation of corrective actions should be introduced incrementally, with risk-proportionate controls.
- Model governance and explainability: Operators and engineers should be able to understand why an AI copilot made a given recommendation. Black-box outputs are incompatible with regulatory accountability in regulated manufacturing sectors.
AI and machine learning technology can help organizations analyze vast volumes of data across their infrastructure in real time to uncover known and novel threats10IT/OT convergence gives malicious actors easier access to previously air-gapped OT environments and exposes legacy systems to modern threats - but that same capability must be governed to prevent the AI layer itself from becoming a liability.
Practical Steps for Secure AI Copilot Adoption
Translating the opportunity into operational reality requires a structured adoption sequence. Piloting without governance architecture in place creates technical debt that compounds as deployments scale.
1. Pilot in non-critical lines first. Deploy AI copilots in production areas where the operational consequence of an erroneous recommendation is limited and recoverable. Use the pilot to validate model accuracy against human judgment before expanding to core processes.
2. Enforce network segmentation for connected worker devices. AR and wearable endpoints should operate in dedicated network zones, segmented from core OT control systems. Apply ISA/IEC 624431cybersecurity analysts tracking OT environments-aligned segmentation principles to all connected worker device traffic.
3. Establish a model governance board. Designate cross-functional ownership of AI model updates, data inputs, and performance thresholds. Governance should include OT security, operations, and IT representatives - not IT alone.
4. Implement continuous monitoring dashboards. Deploy dashboards that expose both operational performance metrics and AI behavioral indicators in a single view. Anomalies in model recommendations should trigger the same escalation workflows as production alerts.
5. Invest in OT-aware security training. The ICS/OT cybersecurity field faces a workforce shortage12Rockwell Automation's OT cybersecurity research, with many sites operating with minimal dedicated OT security staffing. Training programs must extend to operators who interact with AI copilots daily, covering data hygiene, social engineering risks, and the boundaries of AI authority on the shop floor.
6. Validate against OT-specific threat intelligence. Generic threat feeds often miss the nuances of industrial environments10IT/OT convergence gives malicious actors easier access to previously air-gapped OT environments and exposes legacy systems to modern threats. Manufacturers should invest in threat intelligence that includes OT-specific indicators and AI-powered analytics to detect emerging risks targeting their connected systems.
Frequently Asked Questions
What is an AI copilot in a manufacturing context? An AI copilot in manufacturing is a conversational AI layer integrated with operational systems such as MES, SCADA, and quality management platforms. It enables natural-language querying, alert triage, anomaly detection, and guided corrective actions - giving operators and engineers real-time decision support without navigating complex system menus.
How do connected worker devices expand the OT attack surface? Each AR headset, smart helmet, or body-worn sensor deployed on the shop floor represents a new network node. These devices continuously collect and transmit operational data, and - if not properly segmented, authenticated, and monitored - can serve as entry points for lateral movement into OT networks and MES environments.
What governance practices should enterprises apply to AI copilots in OT? Key practices include enforcing least-privilege access to AI services, implementing containerized and auditable AI deployments, maintaining data provenance and model explainability logs, and validating AI recommendations against human checks in safety-critical processes. Continuous behavioral telemetry on the AI model itself is increasingly recommended as a baseline control.
What standards apply to AI in industrial OT environments? The ISA/IEC 62443 framework remains the primary standard for industrial cybersecurity, governing network segmentation and access controls relevant to AI-enabled OT. Regulatory bodies are actively developing AI-specific risk disclosure requirements, and the EU AI Act introduces risk-tiered obligations that may apply to automated decision-making in manufacturing operations.
Conclusion
AI copilots and connected worker platforms represent a genuine productivity frontier for manufacturing operations - one already delivering measurable improvements in operator efficiency, knowledge transfer, and anomaly response times. Yet the same connectivity that enables these gains expands the industrial attack surface in proportion to deployment pace.
For senior operations and OT security leaders, the imperative is not to slow adoption but to ensure security governance keeps pace with capability deployment. Secure-by-design AI models, endpoint governance for connected worker devices, and OT-specific threat intelligence are not post-deployment additions - they are foundational prerequisites. Enterprises that embed security at the core of their AI copilot strategy will be positioned to scale; those that treat it as an afterthought will encounter the consequences in production.
The OT/IT playbook is being rewritten. The question for manufacturing enterprises is whether their security architecture is being updated in the same revision cycle.