A Censys advisory reports that 5,219 Rockwell Automation/Allen-Bradley programmable logic controllers (PLCs) are openly accessible on the public Internet, introducing operational technology (OT) vulnerabilities susceptible to exploitation by Iran-linked threat groups. This finding, issued in response to U.S. joint advisory AA26-097A on April 7, 2026, underscores ongoing risks to critical infrastructure globally and highlights the urgency of asset visibility and network segmentation as key cybersecurity priorities.[1]
Background
The U.S. Cybersecurity and Infrastructure Security Agency (CISA), Federal Bureau of Investigation (FBI), National Security Agency (NSA), Environmental Protection Agency (EPA), Department of Energy (DOE), and U.S. Cyber Command published advisory AA26-097A after incidents involving Iranian-affiliated advanced persistent threat (APT) actors exploiting publicly accessible Rockwell/Allen-Bradley PLCs. Impacted systems include CompactLogix and Micro850 models, which were accessed and manipulated using legitimate Rockwell engineering software, resulting in operational disruptions and financial losses across water, wastewater, energy, and government sectors.[1]
Censys's Internet scan found 74.6% of exposed hosts-3,891 PLCs-are in the United States. Other notable locations are Spain (110), Taiwan (78), Italy (73), and Iceland (36), with potential implications for Iceland's geothermal energy infrastructure.[1]
Details
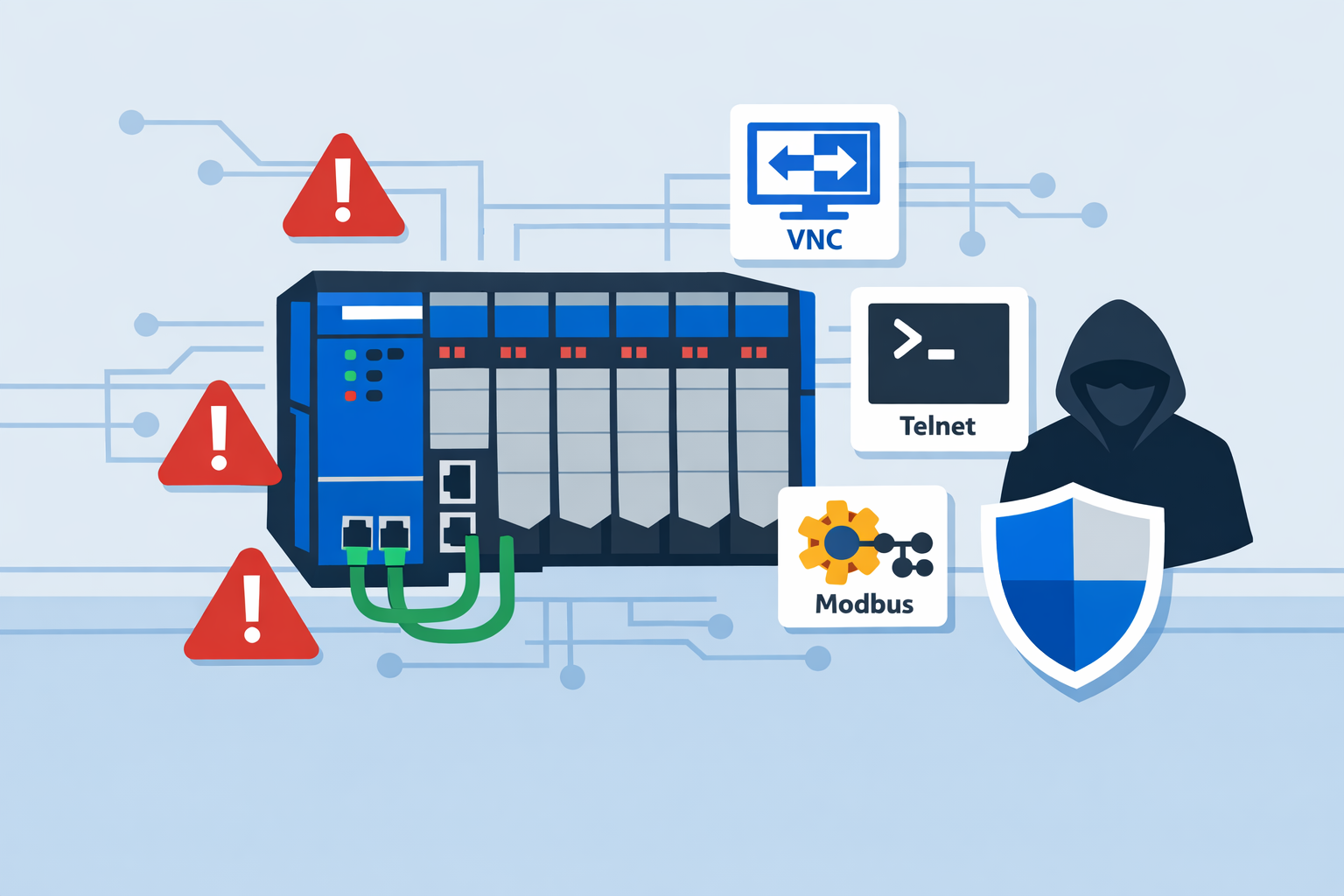
Censys data shows many exposed devices disclose firmware version strings in EtherNet/IP (EIP) identity responses. This unauthenticated information allows attackers to identify and prioritize vulnerable PLCs, such as end-of-sale MicroLogix 1400 models running obsolete firmware.[1] Co-exposed services-including VNC (771 instances), Telnet (280), and Modbus (292)-broaden the attack surface and may permit unauthorized supervisory control and data acquisition (SCADA) or human-machine interface (HMI) access.[1]
Censys also identified operator workstations running the full suite of Rockwell engineering tools-including Studio 5000, FactoryTalk, and RSLinx-exposed to the Internet. These workstations, identified by Windows-hostname product strings and CodeMeter license endpoints, could serve as initial access points to OT networks.[1]
Outlook
Organizations using Rockwell PLCs should immediately remove public Internet exposure, utilize jump hosts or secure gateways for remote access, and disable cellular modems unless essential. Recommended immediate actions include setting PLC physical mode switches to RUN to prevent remote overrides, disabling VNC and Telnet services, and enforcing multifactor authentication for remote OT access. Monitoring EIP identity response changes and updating or isolating outdated MicroLogix firmware are advised as medium-term steps.[1]
Regulators and industry consortia may further stress adherence to OT security standards such as ISA/IEC 62443, require asset discovery, and strengthen threat intelligence sharing. These exposures highlight the ongoing need for improved asset visibility, network segmentation, and coordinated vulnerability management across critical infrastructure sectors.