Eighty-seven percent of industrial operators rate their ability to detect an active OT breach within 24 hours as high. Yet more than half of those same organizations acknowledge relying on IT security tools with limited visibility into OT-specific traffic1IT security tools with limited visibility into OT-specific traffic-and only 16% cite continuous OT monitoring as the actual foundation of that capability. That disconnect may be the most consequential gap in industrial cybersecurity today.
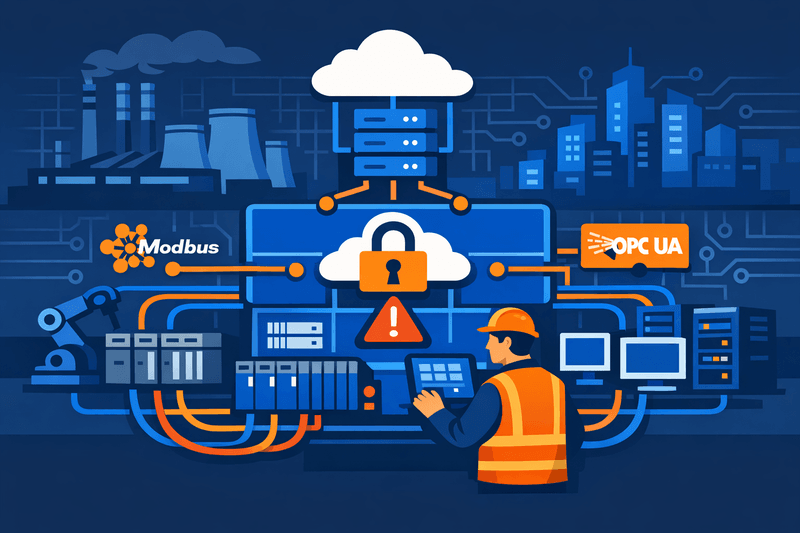
A convergence of recent survey data-including the SANS Institute 2025 State of ICS/OT Security Survey2SANS Institute 2025 State of ICS/OT Security Survey (drawing on 330 industry professionals), the Fortinet 2025 State of Operational Technology and Cybersecurity Report (550+ OT professionals), and a Telstra International/Omdia study of 513 manufacturing respondents-reveals a sector in transition. IT and OT are converging faster than security postures are maturing, and the tools filling that gap were largely designed for a different threat environment.
The Scale of Convergence-and the Risk It Carries
Around 70% of OT systems in companies across the US, Latin America, and Europe are expected to be connected to corporate IT networks within the next year, up from approximately 50% currently, according to the Telstra International/Omdia report3Telstra International/Omdia report. That connectivity delivers genuine operational value: real-time data analytics, predictive maintenance, and centralized monitoring all depend on linking plant-floor systems to enterprise infrastructure.
But the same integration expands the attack surface. Manufacturing has remained the most ransomware-targeted sector globally for the fourth consecutive year, accounting for 26% of all documented ransomware incidents across critical sectors, according to IBM's 2025 X-Force Threat Intelligence Index. In Q1 2025 alone, Honeywell reported more than 2,400 ransomware attacks targeting the OT layer-a sharp upward trend compared to 6,130 such incidents across all of 2024, according to IoT Analytics4IoT Analytics.
Threat actors are increasingly exploiting IT/OT convergence by design. Attackers routinely use social engineering to compromise IT infrastructure, then pivot laterally into OT systems-disrupting physical production for weeks5disrupting physical production for weeks at a time. In August 2025, a ransomware attack on Jaguar Land Rover-traced to a third-party supplier's software-halted manufacturing across three countries for five weeks, with estimated damage reaching £1.9 billion.
Why IT Tools Fall Short in OT Environments
The structural problem is straightforward: IT security tools were designed for IT environments. Only 19% of manufacturing firms surveyed by Telstra International and Omdia are considered "advanced" in securing their IT/OT environments as measured against the NIST Cybersecurity Framework, and a central reason is the mismatch between tooling and environment.
Traditional IT discovery tools typically rely on active network scanning-a method that can disrupt time-sensitive industrial processes, cause unexpected device behavior, and, in worst cases, trigger safety shutdowns. These tools also lack the protocol-specific knowledge to accurately identify ICS devices and cannot provide the PLC configuration details, firmware versions, or backplane-level data that OT vulnerability management requires.
The SANS 2025 data makes the visibility gap concrete. Only 1 in 8 organizations (12.6%) report full visibility across the ICS Cyber Kill Chain-from initial IT compromise through to potential impacts on PLCs, SCADA systems, and physical processes. By Purdue Model level: full visibility at the SCADA/HMI layer (Level 2) stands at just 10%6full visibility at the SCADA/HMI layer (Level 2) stands at just 10%, while coverage at the PLC/RTU level (Level 1) is even thinner.
Organizations with comprehensive OT asset visibility are 3.7x more likely to achieve full coverage across the ICS Cyber Kill Chain, according to SANS 2025 survey analysis-a finding that underscores how foundational the visibility problem is before any downstream detection or response capability can function.
Meanwhile, generic threat feeds frequently miss the nuances of industrial environments. OT systems prioritize availability, reliability, and safety-often running legacy infrastructure that predates modern cybersecurity considerations entirely. Applying CVSS-based scoring without operational context routinely produces poor prioritization. Dragos found that 80% of its 2025 service engagements identified gaps in OT vulnerability management, with limited asset visibility as the primary constraint on risk-based mitigation.
The Segmentation and Governance Gap
Network segmentation aligned to process zones has long been a foundational OT security control, but execution remains inconsistent. The ISA/IEC 62443 zones-and-conduits model7ISA/IEC 62443 zones-and-conduits model and the Purdue Model both frame segmentation as the primary mechanism for containing lateral movement-yet traditional approaches using VLANs, firewall rules, and ACLs struggle in dynamic OT environments where devices change IP addresses and network connections.
A newer class of identity-based microsegmentation platforms addresses this by discovering every device and enforcing policies based on identity and risk context rather than static network boundaries. At the S4x26 conference in February 2026, security professionals demonstrated that integrating asset discovery directly into network infrastructure-rather than applying it as an overlay-revealed previously undetected device communications and enabled real-time, protocol-aware zone enforcement. This approach is reshaping how segmentation is implemented in OT environments.
The governance dimension is equally problematic. The Telstra/Omdia study found that responsibility for IT/OT security is widely distributed and often ambiguous: only 20% of firms identified CISOs as holding primary responsibility. Just 45% of manufacturers surveyed by Telstra International and Omdia were found to be well-prepared for converged IT/OT security across eight key areas, including security networking, supply chain risk, and zero-trust practices. "This responsibility must be clear and integrated so that one group or person will have the authority to act on security challenges for mission-critical systems," according to Geraldine Kor, Telstra International's Head of Global Enterprise Business.
Vendor and Standards Responses
The vendor ecosystem is responding. Purpose-built OT security platforms now offer passive, protocol-aware asset discovery covering industrial protocols-Modbus, DNP3, EtherNet/IP, PROFINET, OPC-UA-without active scanning risk. Siemens' SINEC Secure Connect platform, launched in October 2025, creates a virtual overlay network that allows security teams to enforce granular policy controls without altering the underlying physical topology, directly targeting lateral movement as a primary OT threat vector.
OT-specific endpoint tools such as TXOne Networks' Stellar Discover extend visibility to the endpoint level on legacy systems-including hardware running Windows 2000 through Windows 11-filling gaps that neither network-based OT tools nor corporate IT EDR agents can cover.
On the standards and regulatory side, frameworks including NERC CIP (North America), Australia's SOCI Act, and Singapore's Cybersecurity Code of Practice are expanding, and enforcement is intensifying. The SANS 2025 data shows that regulated organizations demonstrably outperform unregulated peers in detection, containment, and resilience-not because compliance prevents incidents, but because regulatory requirements force deployment of foundational capabilities that also improve response.
Recommendations for Security and Operations Leaders
The emerging industry consensus centers on a layered, OT-aware approach rather than simply extending the IT security stack into OT environments.
Establish and continuously validate OT asset inventories. Passive, protocol-aware discovery tools that provide firmware versions, PLC configurations, and risk context-not just device counts-are essential. Point-in-time inventories decay rapidly; continuous validation is required.
Implement network segmentation aligned to process zones. Segmentation must respect process semantics and operational dependencies. Identity-based microsegmentation, which enforces policies by device identity rather than static IP ranges, addresses the brittleness of traditional VLAN-based approaches.
Deploy OT-specific threat detection down to Purdue Levels 1-2. If visibility stops at Level 3 (operations systems), the environments where PLCs, RTUs, and physical process manipulation occur remain unmonitored. Passive, protocol-aware monitoring at supervisory and basic control levels is non-negotiable for meaningful detection.
Apply OT-specific risk scoring and vulnerability management. CVSS scores without operational context lead to misallocation of remediation effort. Risk scoring should incorporate asset criticality, process impact, and exploitability in industrial environments.
Establish clear cross-domain governance. Accountability for IT/OT security must be explicitly assigned, documented, and tested through OT-specific tabletop exercises and incident response drills that include process engineers alongside IT security staff.
As manufacturers pursue cloud-native MES deployments and edge-enabled operations, the imperative is not to choose between IT and OT security disciplines-it is to ensure OT-specific controls, change management processes, and safety validations are embedded alongside IT-centric capabilities from the outset.