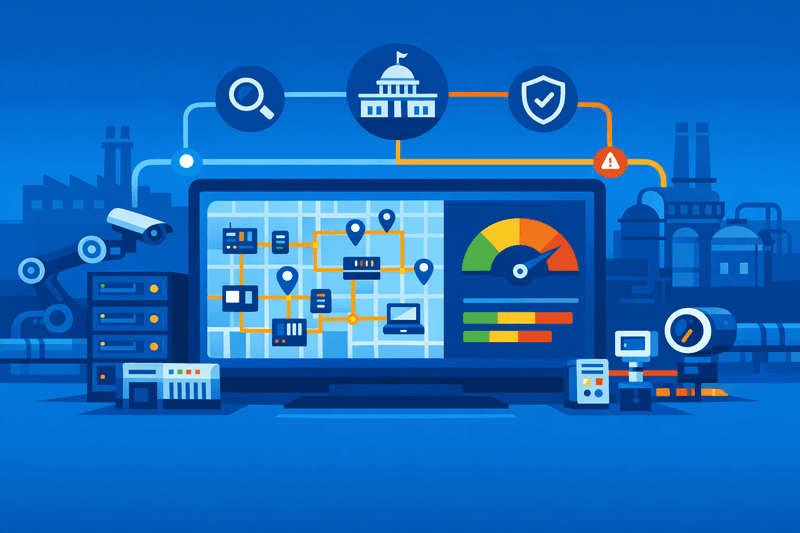
The National Institute of Standards and Technology's National Cybersecurity Center of Excellence (NCCoE) is launching an initiative to close asset visibility gaps in operational technology (OT) environments across critical infrastructure sectors, marking a significant expansion of federal efforts to harden industrial control systems against cyber threats.
Cherilyn Pascoe, director of NIST's NCCoE, announced the initiative after the center completed several prior efforts tied to specific critical infrastructure sectors. The project will establish practical, repeatable methods for real-time asset discovery, taxonomy-based risk scoring, and integration of OT monitoring data with enterprise IT security operations - without disrupting the safety-critical processes that OT systems govern. The NCCoE plans to form an industry-government consortium to advance the work, with pilot deployments spanning manufacturing, energy, and water utilities.
Background
In consultations with multiple critical infrastructure sectors, the NCCoE asked operators about their most significant challenges. Asset management and asset visibility ranked as the top concern across the board, according to Pascoe. The problem is structural: visibility is particularly difficult in industrial control systems due to legacy equipment and distributed environments. Existing asset inventories are often static, point-in-time snapshots stored in documents or spreadsheets that are difficult to maintain manually - especially given that inventories can change frequently.
The NCCoE initiative arrives against a backdrop of intensifying regulatory and inter-agency pressure. In August 2025, CISA - in partnership with the NSA, FBI, EPA, and cybersecurity agencies from Australia, Canada, Germany, the Netherlands, and New Zealand - released joint guidance titled "Foundations for OT Cybersecurity: Asset Inventory Guidance for Owners and Operators." That guidance was designed to help critical infrastructure entities develop and implement OT asset inventories and taxonomies. It was issued ahead of upcoming cyber incident reporting requirements under the Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) and the EU's NIS2 Directive. CISA and several U.S. and international cyber agencies had also previously urged critical infrastructure organizations to inventory their OT assets.
Details
The new NCCoE project will demonstrate "how to do asset visibility in an OT environment," according to Pascoe. The NCCoE plans to launch a consortium with industry and government agency partners, aiming to show how existing standards and frameworks can enhance visibility and how to build an architecture using commercially available, off-the-shelf technologies.
The initiative is described as vendor-agnostic and designed to avoid requiring wholesale platform replacements. Pilot deployments will test interoperable plug-ins for common OT platforms and validate risk scoring that factors in process criticality, asset criticality, and exposure to IT/OT convergence risks. A core strength of the NCCoE model is its capacity to convert high-level guidance into practical implementation assistance by bringing together business, government, and academia to create deployable cybersecurity solutions.
The effort builds on prior sector-specific NCCoE work. In recent years, the center completed a water and wastewater cybersecurity project and released draft guidance to help transit agencies implement the NIST Cybersecurity Framework. A prior NCCoE practice guide demonstrated how energy organizations can use commercially available technologies, consistent with cybersecurity standards, to establish, enhance, and automate OT asset management.
CISA's August 2025 asset inventory guidance was developed through eight collaborative working sessions with approximately 14 organizations and 33 participants, including representatives from U.S. federal agencies and the private sector, covering the oil and gas, electricity, and water and wastewater sectors. Critical infrastructure companies including American Water, British Petroleum, Duke Energy, and Southern California Edison contributed to that guidance.
The NCCoE initiative also addresses governance and information-sharing requirements, including how incident data is shared with regulators and how lessons learned translate into concrete security baselines. Covered entities will need not only to achieve visibility over their OT assets but also to determine whether a cyber incident affecting those assets meets the threshold for mandatory reporting under CIRCIA and the NIS2 Directive.
Outlook
The NCCoE's pilot programs are expected to publish findings and recommended practices later in 2026, with results likely to influence sector-specific guidelines and procurement decisions for OT asset-management tools. Industry observers note that improving OT visibility is increasingly about enabling predictive security - with enhanced network monitoring, behavioral analytics, and asset discovery allowing organizations to identify anomalies before they escalate into incidents. NIST also announced plans earlier this year to update its Guide to Operational Technology Security special publication to incorporate lessons learned, align with related agency guidance, and address emerging risks.