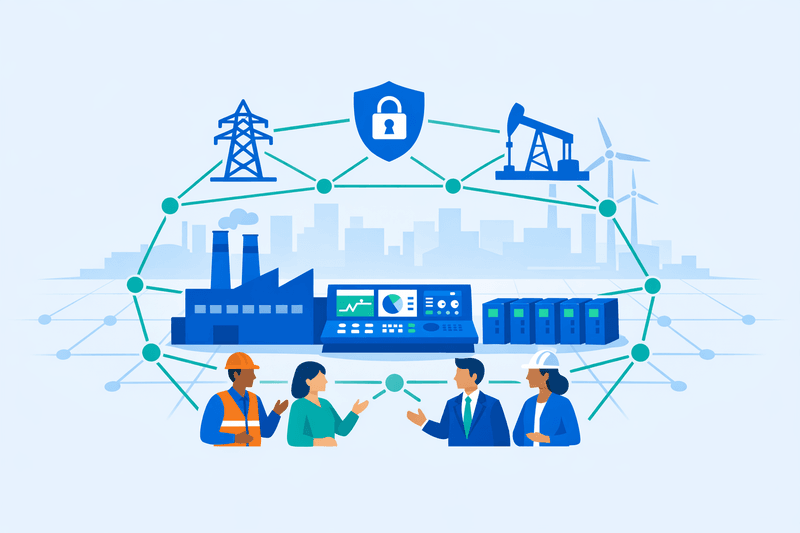
The National Institute of Standards and Technology's National Cybersecurity Center of Excellence (NCCoE) has announced a new operational technology (OT) cybersecurity project focused on asset visibility, marking a shift from sector-specific guidance toward a unified, cross-sector risk management framework. The initiative was disclosed on April 16, 2026, at GovCIO's CyberScape conference in Arlington, Virginia, by NCCoE Director Cherilyn Pascoe.
Background
The initiative arrives amid a worsening threat landscape across industrial control systems (ICS) and OT environments. Forescout Research recorded 508 ICS advisories covering 2,155 vulnerabilities in 2025 - the highest volume since tracking began, with a pronounced spike in high-severity flaws affecting programmable logic controllers (PLCs) and SCADA systems. TXOne Networks reported that 96% of OT incidents in 2025 could be traced to IT system compromises, while Forescout found attacks on OT protocols increased 84% in 2025 over the prior year, with Modbus accounting for 57% of those attacks.
Dragos reported a nearly 95% increase in ransomware attacks on industrial organizations and a 49% rise in ransomware groups targeting OT in the same period. Meanwhile, the manufacturing sector accounted for one in four cyberattacks in 2025, with ransomware attacks on manufacturers surging 61% compared to 46% across all sectors, according to cybersecurity insurer Resilience.
Prior NCCoE efforts were primarily sector-specific, covering water and wastewater systems, transit agencies, and the energy sector. NIST also has an active pre-draft call for public input on SP 800-82 Revision 4, the Guide to Operational Technology Security, which closed February 23, 2026. That process aims to align the core OT security reference document with the NIST Cybersecurity Framework (CSF) 2.0, NIST IR 8286, and SP 800-53 Rev. 5, and to incorporate guidance on emerging capabilities including behavioral anomaly detection, digital twins, zero trust, and artificial intelligence.
Details
Pascoe stated that the new OT visibility project emerged from structured conversations with multiple critical infrastructure sectors. "We had several conversations with different critical infrastructure sectors and asked them, 'What are your biggest challenges?' And across the board, the largest challenge that came up was asset management, asset visibility," she said at the conference.
The NCCoE's January 2026 project portfolio identified OT asset management as a planned technology demonstration intended to provide practical guidelines for achieving and maintaining OT cybersecurity, with a published project description and an open call for industry collaborators expected in 2026.
The project represents a strategic departure from past practice. Previous NCCoE sector efforts - including water and wastewater cybersecurity and transit agency CSF guidance - addressed symptoms within individual sectors rather than the underlying systemic gap: a lack of unified asset awareness across OT ecosystems. The new initiative aims to demonstrate how existing standards and commercially available tools can be assembled into reference architectures applicable across sectors.
NIST plans to form a consortium with industry and government agencies to advance the OT visibility project, with Pascoe noting potential exploration of AI-enabled asset discovery depending on community interest. The project aligns with complementary guidance released in parallel: CISA published its Cybersecurity Performance Goals 2.0 in December 2025, aligned with NIST CSF revisions to address common threats to critical infrastructure. Separately, CISA and international partners released 'Adapting Zero Trust Principles to Operational Technology,' a 28-page guide organized around NIST CSF 2.0 functions and developed with the Departments of Defense, Energy, and State, and the FBI.
Legacy infrastructure compounds the OT security challenge. As Pascoe noted, visibility remains "very difficult" in industrial environments due to legacy systems, distributed deployments, and the prevalence of embedded devices with limited logging and authentication capabilities.
Outlook
The NCCoE plans to publish a formal project description for public feedback and invite collaborators to support the OT visibility initiative in 2026. Adoption timelines will depend on consortium formation and community engagement. Industry observers and standards bodies will watch whether the cross-sector reference architecture can bridge interoperability gaps between NIST guidance, IEC 62443, and existing OT security frameworks deployed by critical infrastructure operators - a prerequisite for broad compliance alignment and measurable maturity benchmarks across manufacturing, energy, transportation, and water sectors.