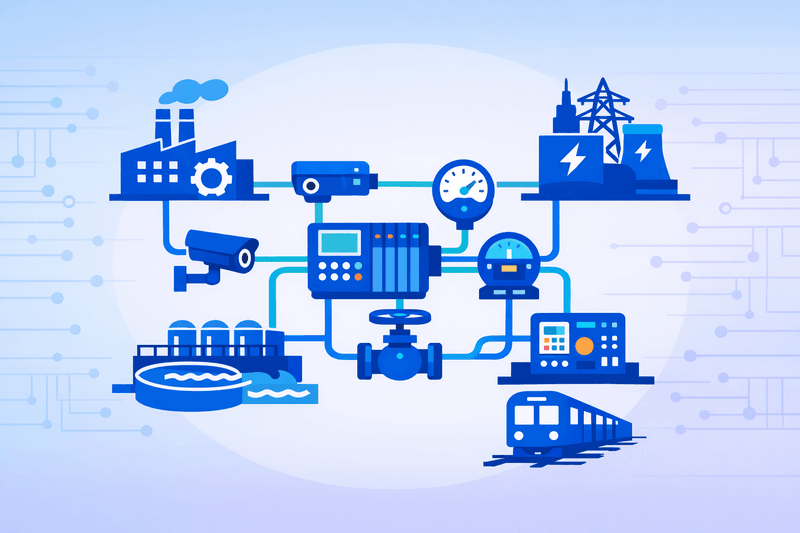
NIST's National Cybersecurity Center of Excellence has announced a cross-sector operational technology (OT) asset visibility project, marking a strategic shift from single-sector guidance to a unified framework for identifying and managing industrial assets across all critical infrastructure segments. The initiative follows consultations with multiple sectors that each cited asset management as their top cybersecurity challenge. It will proceed through a consortium of industry partners and government agencies.
Background
NCCoE director Cherilyn Pascoe disclosed the project on April 16, 2026, at GovCIO's CyberScape conference in Arlington, Virginia, describing it as the product of a deliberate effort to identify the single highest-impact initiative the center could undertake. Prior NCCoE work in OT cybersecurity had been sector-specific - the center produced guidance for water and wastewater operators and released a draft cybersecurity framework document for transit agencies - but those efforts did not address what Pascoe described as a systemic gap. "Across the board, the largest challenge that came up was asset management, asset visibility," Pascoe told the conference audience.
The project aligns with a broader regulatory push. CISA and several domestic and international cyber agencies had previously urged critical infrastructure operators to inventory their OT assets, yet adoption has remained uneven. During a House Homeland Security Committee hearing, Tatyana Bolton, executive director of the Operational Technology Cyber Coalition, stated: "Most sectors have not done an OT asset inventory. So they don't even know what they have." The challenge is compounded by the nature of OT environments: many industrial control systems run on legacy equipment with antiquated protocols that offer limited real-time monitoring capability, minimal logging, and low authentication.
Separately, NIST in January 2026 opened a pre-draft public comment process for Revision 4 of SP 800-82, its Guide to Operational Technology Security, seeking input to incorporate lessons learned, align the document with CSF 2.0, and address changes in the OT threat landscape.
Details
The OT visibility project is explicitly cross-sector in scope, departing from the NCCoE's historical pattern of sector-specific practice guides. Pascoe indicated the center will form a consortium with industry technology providers and government agencies, following the NCCoE's established model of producing reference architectures and NIST Special Publication 1800-series practice guides using commercially available technologies. "Our hope is to be able to demonstrate, how do you leverage existing standards, existing frameworks to be able to enhance visibility?" Pascoe said, adding that AI-assisted visibility capabilities could be incorporated depending on community interest.
The technical barriers are significant. OT environments typically mix embedded devices, programmable logic controllers (PLCs), industrial control systems (ICS), and legacy SCADA systems engineered for reliability and physical safety - not network observability. Inconsistent IT/OT segmentation means anomalous activity can persist undetected for extended periods. The NCCoE's stated approach is to show operators how to build a visibility architecture from off-the-shelf tools rather than requiring proprietary or purpose-built solutions. The project will demonstrate "how to do asset visibility in an OT environment," according to Pascoe.
The threat context is acute. Between March 2010 and January 2026, CISA published 3,637 ICS advisories covering 12,174 vulnerabilities across 2,783 products from 689 vendors, according to Forescout. In 2025, 82% of ICS advisories carried high or critical CVSS severity ratings, and the average CVSS score for ICS advisories crossed 8.0 for the first time in 2024 and remained there through 2025.
Outlook
The NCCoE will form a consortium before advancing the project to an architecture and implementation phase, consistent with its Cooperative Research and Development Agreement (CRADA) model. Pascoe noted the center is also evaluating how AI tooling could augment OT asset discovery and anomaly detection as part of the effort. The resulting reference architecture and practice guide, once published, would provide manufacturers, energy providers, utilities, and other critical infrastructure operators with a repeatable, standards-based methodology for establishing continuous OT asset inventories - a foundational control that most sectors have yet to implement at scale.