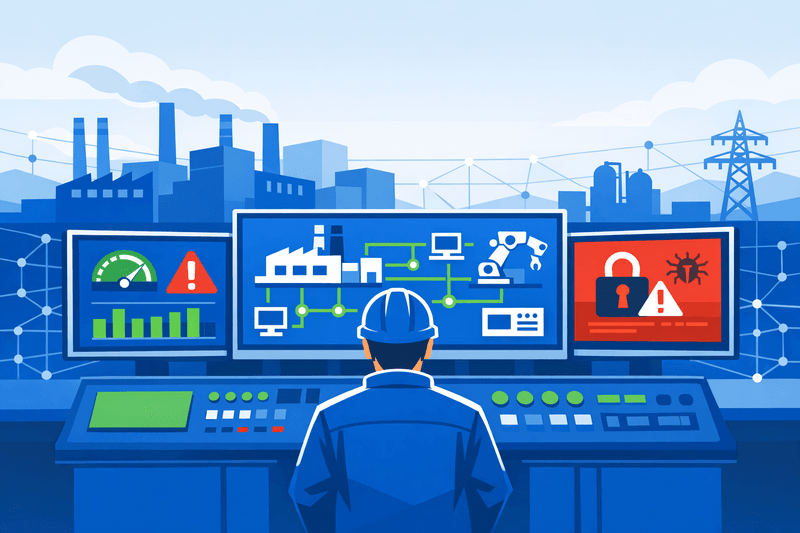
NCC Group has warned that ransomware attacks on operational technology (OT)-heavy industrial environments are intensifying as IT/OT convergence widens the attack surface across manufacturing, energy, and critical infrastructure. Industrial organizations experienced 2,073 ransomware attacks in the 12 months to March 2026, making industrials the most targeted sector every month during the period and accounting for approximately 30% of all ransomware activity, according to NCC Group. The firm identified escalating IT/OT integration as a core driver, with enterprise network breaches giving attackers a pivot point into production and control systems.
Background
The convergence of information technology and operational technology-once kept largely air-gapped-has steadily expanded the cyber-attack surface for manufacturers, utilities, and critical infrastructure operators. As industrial organizations connect SCADA (supervisory control and data acquisition) systems, manufacturing execution systems (MES), and programmable logic controllers (PLCs) to enterprise IT networks, threat actors exploit weakly segmented environments to escalate from IT compromises into OT disruptions.
NCC Group data shows that ransomware activity against industrial organizations rose more than 87% in 2024, alongside a 60% increase in ransomware groups actively affecting OT and ICS environments. Dragos, which tracks industrial-specific threat activity, recorded 708 global ransomware incidents impacting industrial entities in Q1 2025 alone, up from approximately 600 in Q4 2024. The threat is compounding: Dragos tracked 119 ransomware groups targeting industrial organizations across 2025, collectively impacting more than 3,300 industrial organizations.
A structural vulnerability underpins the surge. According to a Ponemon Institute survey of 1,056 global IT and security practitioners, 73% of respondents said their organizations lack an authoritative OT asset inventory. This visibility gap allows ransomware to propagate undetected across OT networks before operators can intervene. NCC Group's Sean Arrowsmith, Director of Industrials, has noted that asset inventory practices common in enterprise IT "don't necessarily exist in OT in a lot of cases." OT systems habitually run on unpatched, outdated, or out-of-support operating systems, often within flat networks, making traditional vulnerability management insufficient.
Details
Within the capital goods category, machinery sub-sectors recorded 442 ransomware attacks and construction and engineering recorded 394 attacks in the 12 months to March 2026, according to NCC Group. The pattern confirms that OT-dependent environments remain primary targets for ransomware operators seeking operational leverage.
"Our data shows that many organisations continue to prioritise IT security while underestimating the exposure of their operational environments," said Ray Robinson, OT Director at NCC Group. "When OT systems are disrupted, the impact goes far beyond data loss-production can halt, essential services can be disrupted, and in some cases, lives can be put at risk."
Dragos analysis reinforces the attack mechanism. Threat actors increasingly use IT network footholds to pivot into OT-adjacent virtualization infrastructure: in one documented case, a Fog ransomware affiliate used compromised VPN access to reach an ESXi hypervisor supporting SCADA virtual machines, removing operator visibility and control without touching a single PLC or field device. Attackers are also exploiting ERP platforms, MES servers, and remote access infrastructure as high-value targets, because disruption at these layers can translate directly into production shutdowns and supply-chain impact without requiring direct ICS network access.
Nation-state threat actors compound criminal ransomware pressure. According to the U.S. Office of the Director of National Intelligence, China, Russia, Iran, and North Korea continue to target industrial and critical infrastructure systems-collecting intelligence, creating options for future disruption, and, in some cases, pursuing financial gain.
In response, NCC Group and Dragos announced a joint IT/OT convergence incident response retainer service, combining NCC Group's Digital Forensics and Incident Response (DFIR) capabilities with Dragos's OT expertise and the Dragos Platform to deliver end-to-end incident response across both IT and OT estates. For OT-specific resilience, NCC Group applies the SANS ICS Five Critical Controls framework, which encompasses ICS-specific incident response planning, defensible architecture design, continuous ICS network monitoring, secure remote access methods, and ongoing security awareness programs. Regulatory pressure is also intensifying: the EU's NIS2 Directive and Cyber Resilience Act, alongside NIST Cybersecurity Framework guidance, now explicitly include OT environments within the scope of cyber resilience obligations.
Katarina Sommer, Global Head of Government Affairs and Analyst Relations at NCC Group, stated: "Organisations that focus compliance efforts solely on IT risk are exposing themselves to operational, regulatory and safety consequences."
Outlook
Ransomware activity targeting industrial organizations is expected to intensify as adversaries increasingly focus on IT systems that underpin OT operations, according to Dragos analysts. Threat intelligence firms project a continued shift toward AI-driven campaigns, faster execution timelines, and extortion-only models that bypass encryption in favor of data-theft leverage. Supply chain attacks on industrial organizations nearly doubled in 2025, rising from 154 incidents in 2024 to 297, as attackers exploited third-party vendors to reach larger targets. For operations and security leaders, closing the OT asset visibility gap-through passive network monitoring and a comprehensive asset inventory program-is identified by both NCC Group and CISA as the foundational step before segmentation and incident response investments can deliver measurable risk reduction.
For more on how the Dragos 2026 OT Cybersecurity Year in Review maps these trends, see Systemic Risk Rises as OT Security Gaps Persist in 2026 and Threat Actors Target OT/CP Networks as Industrial Segmentation Gains Urgency.